Blockchain Technology Basics and where Bitcoins Come From
Since 2009, and especially in the last two years, we have been hearing curious words such as “cryptocurrency,” “bitcoin,” and “blockchain” thrown about... These evoke a feeling of mystery in most people, as if they were spells or magical incantations for those who are in the “circle of trust.”When you try to learn more about bitcoin by asking people, you hear enthusiastic descriptions such as “this is revolutionary technology,” “a breakthrough,” “the financial system of the new world,” “a global turning point,” and so on. The truth is that not many people understand what blockchain technology is, how it works, where bitcoins come from, or the advantages and disadvantages of this algorithm.
We will try to answer these questions without sophisticated mathematics but with simple examples and associations. We hope that, by the time you have finished reading each article in our series, you will know more about bitcoin, cryptocurrency, and the blockchain than the average person.
Many people think that bitcoin and the blockchain are the same thing but named differently – this is not true. Bitcoins are a product of the blockchain. The blockchain is technology that could be used in many spheres such as medicine, logistics, banking, defense, etc. It is simply a method of recording and transferring information. Some people even believe that army scientists invented it in the 1980s, not Satoshi Nakamoto & Co in 2008. This premise is based on the notion that the military needed technology, which could guarantee the survival of at least one information block after an attack such as nuclear war. The blockchain is indeed perfect for this purpose because it logs identical copies of all the transactions ever made in the system (e.g. members, defense points) throughout the entire network. Since the blockchain is a single-level net without a center, any member (i.e. block) of this network can access the same information.
As you can understand, if even 99% of this network was destroyed, the army and defense systems would still have access to all the information they needed. This is why this technology is called “blockchain,” because it is essentially a chain of blocks. We will explain this concept step by step, starting with a simple example, which will explain how the blockchain works.
Let’s imagine that you and your friends decided to create a private financial system, which will be used only by your narrow circle and without real money. You would need to create some type of virtual currency – either electronic (meaning on the net) or on paper. Let’s say you decided to do this using paper. So, the entire group gets together for a picnic in the park, where you enjoy the sun and fresh air. At some point, you decide to make your idea of a virtual monetary system a reality. Using chalk, you draw a table on the ground where each person writes down his/her surname, the number of coins that he/she has, what money he/she recently transferred to others, and everyone in the group signs it by hand.
The table looks nice. You could walk through the park and nobody can change your position on the table because you signed it by hand. The system works – you just have to come to the park from time to time, in order to record any changes made in the table. You overlooked one thing, however... Suddenly, it starts raining and all the data is washed away.
Faced with this problem, the group decides that each friend will log any transactions they have made (e.g. payments) and keep a record of the total balance, which results from these transactions. Then the question arises: How do you inform others about transactions that were made by you? To address this problem, you decide to record each transaction in a separate note and then show all the notes to every person in the group so they can record them in their own logs and calculate the new balance of coins. You also agree that each transaction would be signed by person who made it, using a digital signature. Clear enough so far, right?
How a digital signature works – The first technical issue
In the digital world, any person can generate a “digital surname” and a “digital signature,” that is to say a digital public key and digital private key correspondingly. The “digital surname” is visible to anybody but the “digital signature” is kept secret. As a result...- You can write messages, sign them with your “digital signature,” and publish them on the net.
- Everybody can see that a message was written by a person with a particular “digital surname” because it was signed with their unique “digital signature.”
- The “digital signature” is so unique that no one can forget it.
- One person can generate many surnames and signature sets, with each set used for a different purpose.
How blockchain transactions are organized
Let’s say 10 friends are taking part in the virtual monetary system that was devised in the park. This means that 10 transaction notes will be generated simultaneously. Also, it is unclear who has already recorded the transactions in his/her own log and who has not. Which notes have been recorded by everyone and are, therefore, no longer needed? For example, how can Andrew be sure that John has 30 coins to complete an upcoming transaction and has not already spent them?To answer these questions we need to explain the second technical issue – the so called “hashing procedure.”
What is hashing? How does hashing work? Why do we need hashing?
Hashing does two jobs: one, it compresses information, reducing its volume and accelerating the transfer speed; two, it encrypts information. It all sounds rather complicated but we will explain by using a simple example.When I was a kid, my friend and I loved playing “spies.” We invented a cryptography code to keep our correspondence secret. Since there was no email yet, we would leave notes for each other in a post box. We would write words using numbers. For example, 1 was assigned for “A,” 2 for “B, ” 3 for “C,” and so on. In order to send a note with the word “hello” to my friend, I would write it as a sequence of numbers 8-5-12-12-15.
Nowadays, when you send information in a digital format, how do you know that the recipient will get the exact message that you’ve sent or that your message wasn’t intercepted and modified on the way?
The simplest way to check is to ask for the message to be sent back to you so that you can compare it to the original. If something went wrong only on the way back, however, you wouldn’t know whether the original message was sent correctly. This is one problem with this verification method but here is another: The original message might be big, HD video, for example. If we had no other way of verifying that the correct message was delivered, we would have to send it back to the recipient every time.
There is a simpler way to do this – by simultaneously compressing and encrypting the message.
Let’s return to the childhood spy game for a moment to give you an example of compression. If I multiplied the numbers in the word “hello” (8x5x12x12x15=86,400) and sent not only the word “hello” but also the 86,400 code to my friend, he could check whether my initial message was transferred to him unchanged. If a hacker modified message to “hey” en route, my friend would receive the compression H(7)xE(5)xY(24)= 840, notice the mismatch, and we would both know that something was wrong.
Compression doesn’t protect information, however; it only makes it lighter for transfer by shrinking its size. That’s why, in our example, hackers could mix letters but the encryption would remain the same if, for example, “hello” was changed to “lhelo.” That’s why compression requires encryption. Modern software uses more sophisticated algorithms to accomplish this system of “letters’ multiplication,” making sure that initial message’s compression code changes with even the slightest interference. Besides, it is almost impossible to crack the message or to get same compression (encryption) code. Or it would take too long to do so. This compression method is called “crypto secured.”
For instance, if we applied the well-known SHA-1 algorithm, which was invented to produce compression “encrypt codes,” the message “hello” would look like this: f7ff9e8b7bb2e09b70935a5d785e0cc5d9d0abf0.
If someone intercepted the message and modified it to “lhelo,” my friend would receive a different code: 2d99afdcfead08f7301d3009da70edd1b3c97c40. As you can see, it looks nothing like the “hello” code. Pretty simple, right?
To recap, hashing is a procedure of compression and encryption that keeps information safe and catches any cracking/hacking attempt.
Now that we have an understanding of that, we can go back to our topic – How is the blockchain organized?
To avoid the above mess, the group of friends decide to exchange not only the paper notes which log their personal transactions, but also entire pages of the log. For example, Jeff has accumulated a lot of single notes, accurately recorded them in his register, numbered the page, calculated the hash and wrote it down at the top of the new page. Then he sends the new page to all the friends in the group.
When anyone receives this new page, he/she can check the hash of the previous page and the page number – this should be a completely new page, not an old page which has been re-written. Also, he/she needs to be sure that everyone in the group holds the exact amount of coins specified on the new page. To check this, he/she would have to re-read the entire log (i.e. all the pages) and re-calculate all transactions. This task would be difficult and time-consuming, unless it was done by a computer.
If everything matches – that is to say the amount of coins held by each person and the hash of the previous page – each friend would insert Jeff’s page into their log. Separate notes, which were already recorded on this page, would be discarded and the page would be sent to the others.
If something was wrong on Jeff’s page – either the amount of coins was not confirmed by the re-calculation of all transactions or the hash code didn’t match previous page – the person would ignore this page. From this example, we understand that the entire set of numbered pages that record all transaction is the blockchain.
How do new blocks appear in the blockchain? What does “bitcoin mining” mean?
What would happen if every friend in the group started writing on page #10? Well, they would end up with ten different pages named #10. Which one would be the correct one?First of all, every new page should be created within 10 minutes. This is amount of time needed to inform everyone that a new page has been formed.
Second, a few friends who are randomly selected are in charge of the new page. How is that random selected made in bitcoin technology?
The choice is made by solving riddles or performing tasks, in this case, maths. Whoever calculates the solution first, he/she would take all the paper notes and consolidate the information in a new page. While the others are still solving the task, the new page will be distributed among the group and a new task will be set.
This algorithm works very well until we realize that one friend, John, solves tasks much faster than the others. John is a mathematician so it’s much simpler to him to solve the tasks. His friends begin to worry that John will end up taking control of more than 50% of the financial system because he is solving tasks faster than everyone else. In other words, John will be “processing” more than 51% of all the pages. This will give him the opportunity to block other members from making money transfers because he is creating the majority of new pages and appointing hash. For example, he can write an alternative log, which will show that John didn’t send money to anyone (i.e. this new fake history would cancels all of John’s transactions, restoring all his money as though it was never spent). Then he could present this longer fake page to the group.
Blockchain is built in such a way that, if any problem with the sequence of pages arises, it assumes that the “correct” log is the one with the longest chain of blocks (pages). This is the well-known so-called “51% attack” problem of blockchain technology. We will discuss this further in a special article in the future.
Finally, the solution to the task should also be recorded on the page, since it has a specific relationship to the pages in the blockchain. This is done to avoid cracking page arrays, for example from page #10 until the most current page. In this case, too many tasks are required to be solved in a very short time.
Here, we discuss another “mysterious” process – bitcoin mining, which is a process of “task solving” as per our example.
How does money magically appear through mining process? Where do bitcoins come from?
Initially, it was possible to distribute coins among the lucky friends on the first page, but that was not fair. In order to involve more participants, an agreement was made to gradually distribute coins to those who create the page, i.e. those who solve the task correctly. If a member wrote on the page “give me 50 coins from nowhere,” the page would be treated as wrong and not accepted by the others. Also, it was agreed that within first couple of years, 50 new coins would be created per new page, and that the number of coins would reduce to 25 later on. As a result, the total amount of bitcoins is increasing but, ultimately, there can be more than 25 million bitcoins altogether in existence. At this point in time, approximately 15.2 million bitcoins have been issued: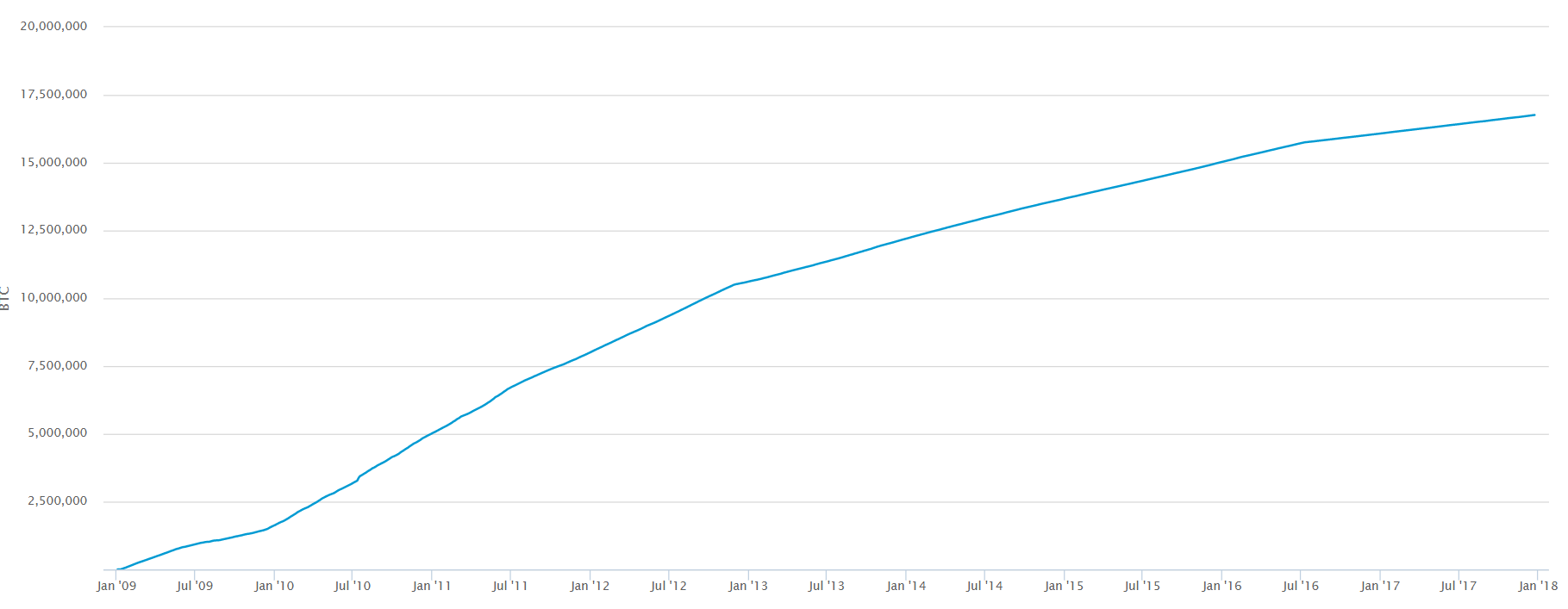 Source: www.quorra.com
Source: www.quorra.com Due to this feature, more and more people want to join the process in order to get coins, especially since later on fewer coins will be distributed per page. Also, people endeavor to solve tasks faster, because the faster they solve the task, the better their chances of creating a new page and getting coins. This is why these massive bitcoin forms are being created. The more processing power one such farm possesses, the more it increases its chances of solving tasks and being rewarded new coins.
Another aspect of this is process is the creation of processing groups, or “mining pools,” where a large number of independent computers “pool” their processing power and work together as one massive center. This also increases the chances of getting coins by solving tasks faster. The earned coins are divided proportionally among all group members. At this time, Chinese pools control 81% of the global network rate.
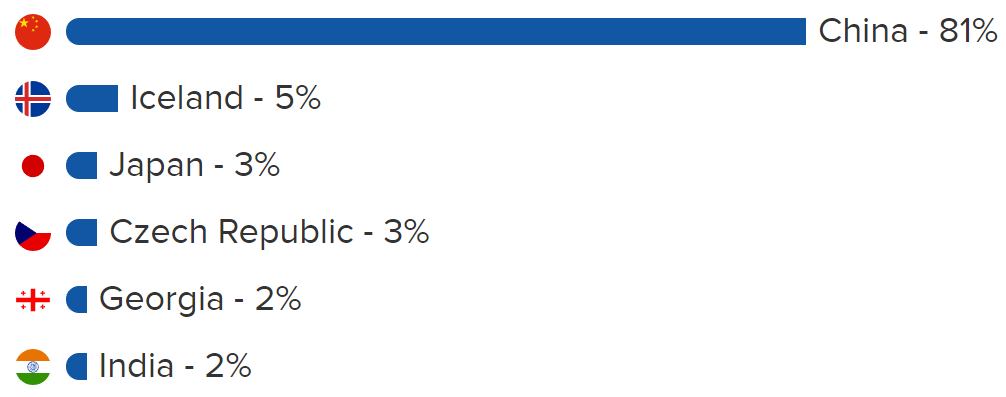
Source: buybitcoinworldwide.com
As more and more people want to get their hands on the so-called “currency of the future,” crypto fever spreads far and wide. However, since only 25 coins are distributed every 10 minutes, this has led to exchange and trading, where coins are either exchanged for fiat money or traded. Trading first started on MT Gox (this is a different story how it has collapsed), and now it is on Luxembourg exchange. One month ago, the CME Group launched BTC futures trading. This is done for those who want to own bitcoin but have no desire or opportunity to mine it (i.e. solve tasks so that they can be involved in new “page” formation). At the same time, many online stores and services are beginning to accept bitcoins as payment – this is another way that people are using to collect bitcoins.
Now you know more about bitcoin and the blockchain than most people around you. As with any other technology, bitcoin has advantages and flaws. This is the topic that we will touch on in our second article “Blockchain and bitcoin imperfections.”